Telegram as a Weaponized Channel. What the FBI Flash Means for Modern Cyber Risk
The recent FBI Flash advisory highlights a pattern that many organizations still underestimate. Threat actors linked to Iran are using Telegram as command and control
Modern Threat Reality. Why Adversaries Win Through What You Ignore
There is nothing surprising about foreign threat actors maintaining access inside U.S. networks. That has been the baseline for years. What makes this moment different
Cyber Power and National Security. What America’s New Cyber Strategy Means for the Future
Cybersecurity is no longer a technical issue reserved for IT departments. It has become a central pillar of national security, economic stability, and global geopolitical
CMMC 2.0 Readiness. How INFOWATCH LLC Supports Defense Contractors
Cybersecurity Maturity Model Certification 2.0 is the Department of Defense’s updated framework for protecting Federal Contract Information and Controlled Unclassified Information across the defense industrial
Cybersecurity in Africa. How Well Is the Continent Matching Global Standards
Africa’s digital growth is accelerating at a pace that was unimaginable a decade ago. Mobile internet penetration continues to rise sharply, fintech services now power
Ghana’s Cybersecurity Act: How Well Does It Match Global Standards?
Introduction Cybersecurity has become a core part of national strength. Countries across the world now rely on strong digital systems to protect their economies, government
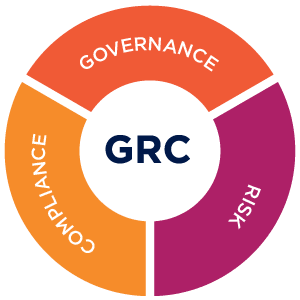
Why GRC Is the Backbone of Today’s Cybersecurity
Modern cybersecurity is no longer only about firewalls, antivirus tools, and technical defenses. Today’s threats move faster, hit harder, and target every layer of an
Breach of Chinese Cybersecurity Firm Exposes State-Backed Hacking Tools: Implications for Global Cybersecurity
Introduction On November 10, 2025, a major cybersecurity event shocked the global tech and intelligence community. Knownsec, a prominent Chinese cybersecurity firm with strong ties
The Cost of Cybersecurity for Small Businesses (SMBs)
In today’s digital world, cybersecurity is no longer optional—even for small businesses. Cyber threats are evolving, and small businesses are increasingly becoming prime targets for
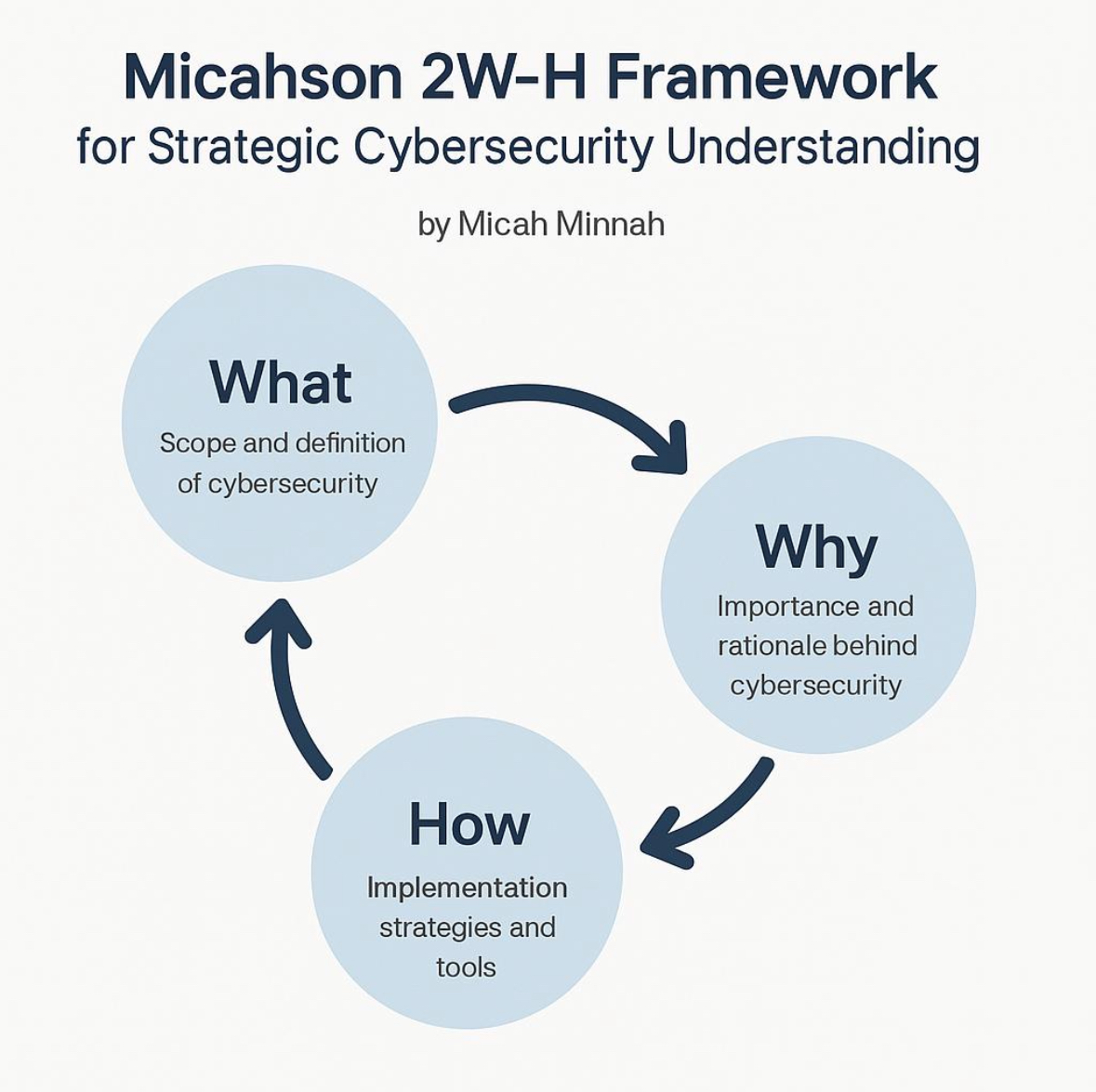
Micah Minnah’s 2WH Framework: Bridging Classroom Theory and RealWorld Cybersecurity Practice
Cybersecurity continues to evolve at a breathtaking pace, driven by increasingly sophisticated threats and complex organizational environments. Yet, despite the proliferation of degree programs and
- 1
- 2